Every October the CyberSecurity & Infrastructure Security Agency (CISA) releases a list of resources and tips for National CyberSecurity Awareness Month – which is now in its 18th year.
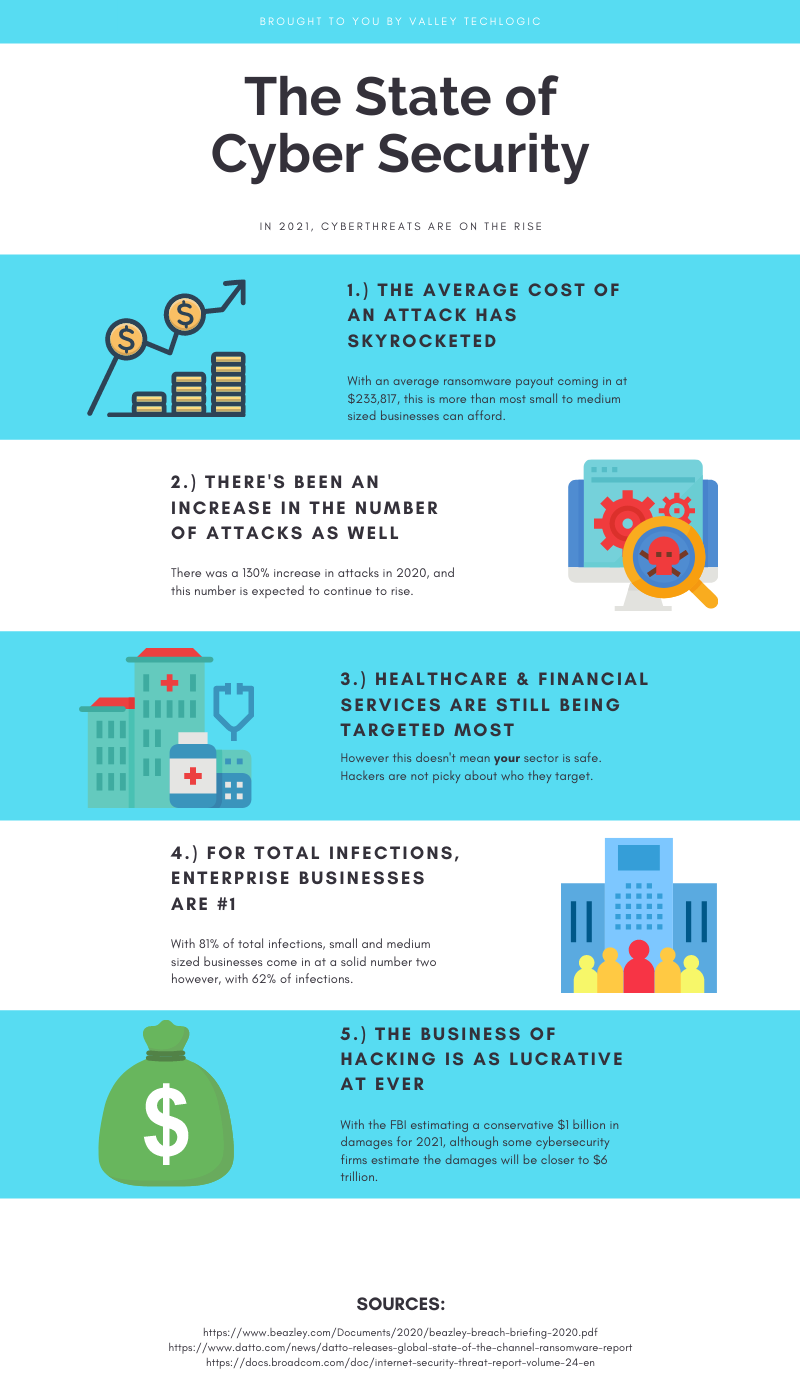
This year’s theme is “Do Your Part. #BeCyberSmart”. There has been an onslaught of news worthy ransomware attacks, DDoS attacks and data breaches (up 38% this year compared to last) in 2021 and there has never been a better time to address what the average person or business can do so they don’t end up as part of these statistics.
We’ve created this checklist so you can see if you’re following the right path to keep your business safe from outside intruders.
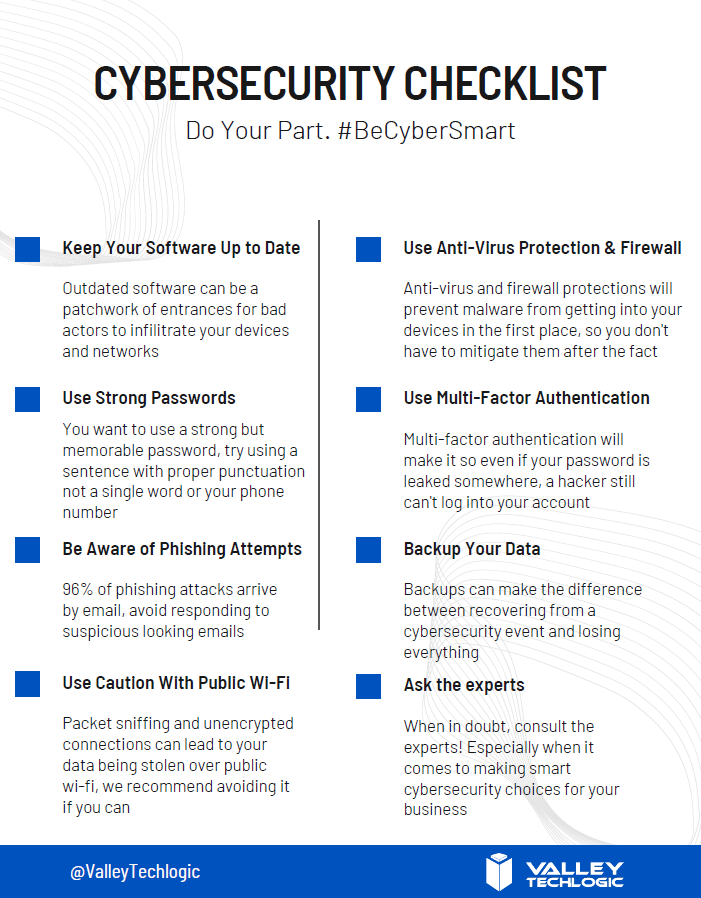
Cybersecurity requires ongoing maintenance to succeed. Following simple safety steps will help but it’s important not to disregard active threats to your business from the outside.
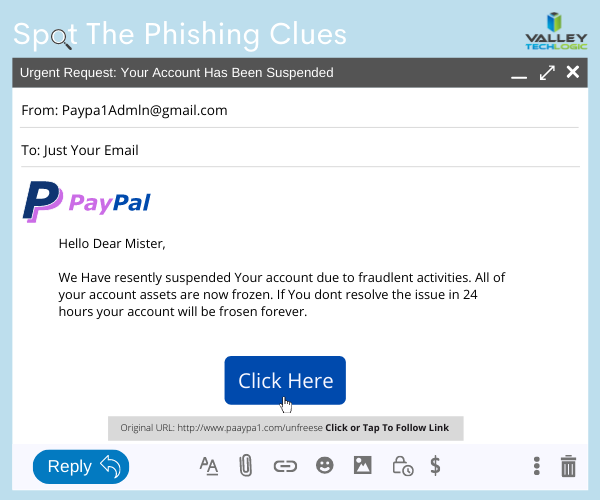
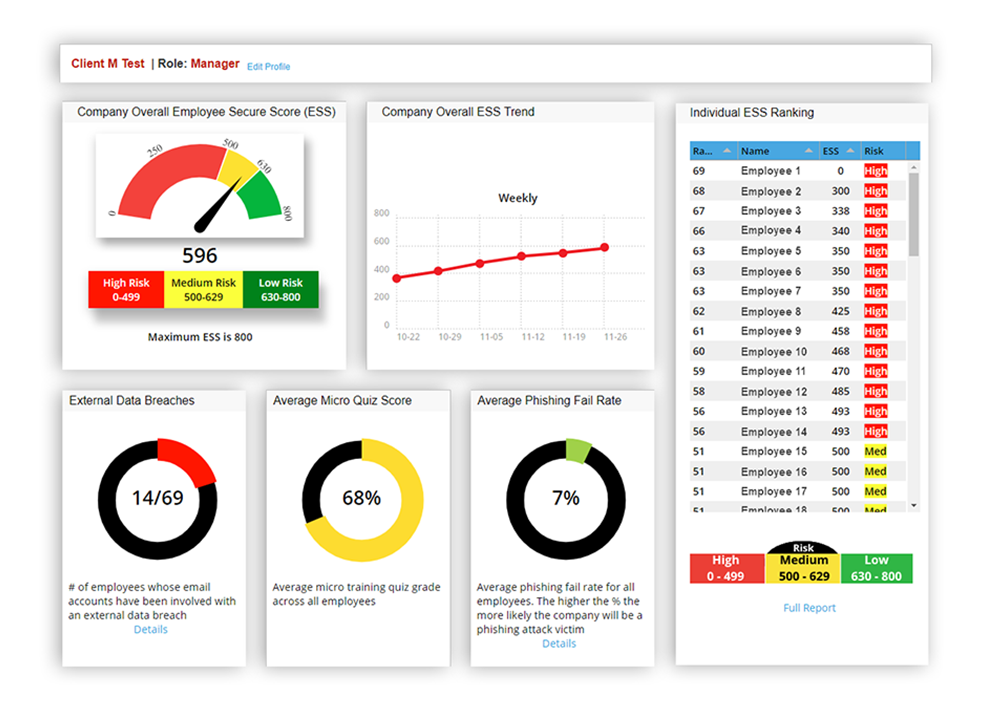
Ongoing employee training is one way to combat those threats, cybersecurity training has evolved to include bite size doses of good advice for your employees that could make the difference between inadvertently falling for a phishing scam or attack attempt and reporting it to your IT team as they should. 95% of data breaches involve human error.
It can also be important to have a team behind you making sure all of your company devices are maintained and updated, even if that outdated Windows 7 computer that sits in a corner is barely used it can still be a threat to your business. Older devices with outdated software can act as a gateway to allow bad actors into your business.
More advanced maintenance such as enabling two-factor or multi-factor authentication on company accounts can be another important step to keeping threats out. If someone gets your password from another company’s data breach (which happens all the time) that phone pop up could prevent you from being hacked.
Finally, having a comprehensive backup program for your businesses data is the final shield against cyber threats. We’re unique in that we offer not only active backups but archival backups as well. The archival backup is “Write once, Read many” which means you can look at the data as often as you like but it can’t be edited or deleted.
A bad actor may find your unbacked up data, and they may gain access to your active backups, but that archival data is virtually bullet proof. For your important files, the ones that must not be deleted at any cost, having that backup there and ready if you need it is the peace of mind most of us would not want to be without (learn more about our backup program here).
If this article has gotten you thinking about what you can do to improve your cybersecurity processes or even that you need to create a plan to get there, we’d love to help. Schedule a discovery call with us to learn more about how Valley Techlogic can help you be #CyberSmart.
Looking for more to read? We suggest these other articles from our site.
-
Yesterday, Facebook experienced their worst outage since 2008
-
The global chip shortage timeline of events, and when it could end
-
Microsoft 365 and Office 365 prices are going up, when and by how much?
-
6 Fantastic things a great MSP can do for your business
This article was powered by Valley TechLogic, adns, n IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.





 Even detection’s
Even detection’s 




