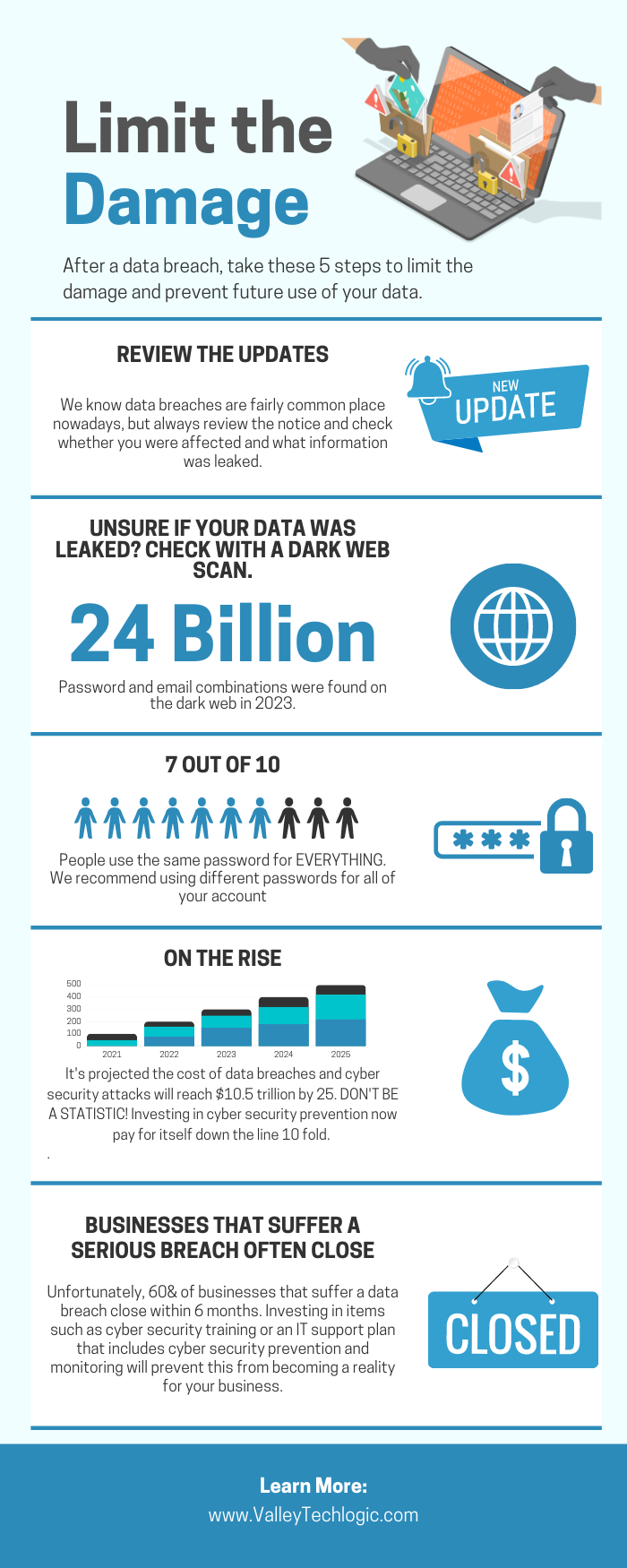
We’re all familiar with the usual suspects when it comes to cyber threats, viruses, trojan horses, phishing attacks, malware and ransomware. We’ve covered these threats in great detail (here’s just a few articles on these topics: 10 scary cybersecurity statistics business owners need to know, Zero trust or zero effort, how does your businesses security stack measure up?, Can you spot the phishing clues? And 10 tips to avoid falling for a phishing scam). Even if you’re not a technical inclined person you probably have some awareness of how to avoid these threats, such as being careful with suspicious emails and attachments or not downloading files from unknown sources.
What about emerging cyber security threats? These are threats that are not well known and in fact may use improvements in technology such as AI (artificial intelligence) to their advantage for nefarious gain.
Bad actors are continuously looking for new ways to subjugate your devices and gain access to your systems and data to exploit it for their own gain, and unfortunately in 2024 we don’t believe things will be any different.
Knowledge is power, so by being aware of these emerging threats you can learn to avoid them or learn what protections you need to put in place to prevent yourself and your business from becoming a victim.
Here are five emerging threats that we believe will grow in popularity in 2024:
- Supply Chain Attacks: Cyber criminals have learned targeting vulnerable systems that supply the things we need day to day (for example the Colonial Pipeline attack that occurred in 2021) can result in lucrative payouts as the vendor(s) scramble to get things back up and running again. We’re expecting these types of attacks to continue to increase in 2024.bio
- Biometric Data Threats: As more biometric data is used to confirm your identity for accessing your accounts or making payments, more regulations need to be put in place to protect that data. Facial recognition and fingerprint scans can often give someone access to your personal devices (such as a cellphone) and those devices can be the keys to the kingdom when it comes to accessing your accounts. Attacks in 2024 may escalate not just to the theft of data but also physical theft in unison on high value targets (think CEOs, Presidents and other C-Suite users).
- Artificial Intelligence (AI) Manipulation: As more and more people explore using AI in their business or to provide solutions to common problems, there will be more and more bad actors trying to exploit it. We’ll see increased attacks using AI including data manipulation (feeding AI erroneous results so that users are receiving incorrect information) and attacks on systems using AI or powered by AI.
- 5G Network Vulnerabilities: As 4G continues to be phased out and 5G becomes more common place we’ll see increased attacks aimed at these networks, especially as more and more businesses in rural locations utilize 5G as a solution to spotty or absent cable or fiber options in their area. As the nature of 5G is aimed at providing a geographically robust internet solution to companies like these it’s important to make sure your security settings are beyond reproach to inhibit attacks on your network from the outside.
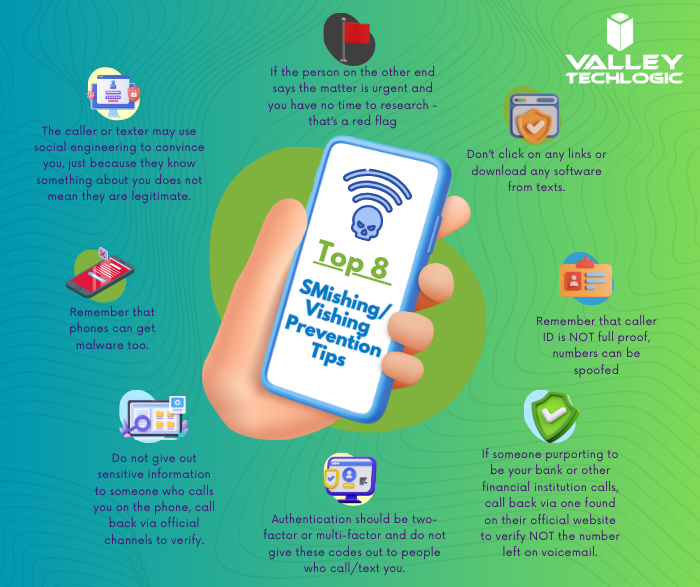
- Advanced Ransomware & Phishing Attacks: Ransomware and phishing attacks are not new, but they continue to grow more sophisticated as as-a-service models continue to roll out, this allows attackers that may not have a firm grasp of technology or even English to send out widespread attack emails that are indistinguishable from emails you may get from reputable services you use for a relatively small monetary fee. Also, because many of these attacks originate outside the US you may have no recourse if your business is successfully hit by one.
These are just five emerging threats but there are many threats out there making it all the more crucial you have a cyber security solution behind your business that’s staying ahead of these threats and more.
The threats mentioned above are crimes of opportunity and it’s very easy to be caught in the wide net that’s being cast by those with ill intentions. Valley Techlogic has been at the forefront of providing all encompassing security solutions to our customers. If you would like to learn more about protection your business from cyber security attacks in 2024 schedule a consultation with our experts today. Also for a limited time when you hear us out, you can also take advantage of our Black Friday offer.
 Looking for more to read? We suggest these other articles from our site.
Looking for more to read? We suggest these other articles from our site.
-
Inclement weather, solar flares, earthquakes – how disaster proof is your businesses technology?
-
Traveling for the holidays? Take 8 tech tips from our experts with you
-
If you have a computer or server with an Intel Processor, you need to patch for this vulnerability ASAP
-
10 Microsoft 365 tools you need to take advantage of TODAY
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.