If you’re using a free email service such as Gmail, Yahoo, Hotmail or even AOL – it’s probably time to make the move to using your business’s domain instead.
We understand it can be hard to let an email you’ve been using for a long time go, and there can be some growing pains when you make the switch. Your existing customers and business associates know you by your existing email address, you may have it organized the way you like it. It can seem like a hassle, but there are some big reasons to make the switch.
- You get what you pay for (in terms of support). Your free email box will also come with non-priority support from your service provider, if you have an issue even if it’s urgent you will still need to get in line with everyone else.
- It’s a target for hackers. Hackers love free email accounts because their popularity makes them ubiquitous. When they access one used by a business, it’s even better.
- Your email is more likely to be marked as “spam”. This is because spammers also use free email accounts to conduct their business, so your emails will just get lumped in with theirs.
- You’re missing out on a business opportunity. Your free email domain doesn’t advertise your business to your customers, it advertises Google, Yahoo, etc.
- It could be seen as unprofessional. Your customers may wonder why emails from you come from a free email provider instead of your domain, even if they never say it.
Even if we haven’t swayed you to make the change, you can still get your email domain established and try to slowly work it into your work routine to send some emails from that domain or switch some of your business accounts to using that email instead.
If you are ready to make the change, we have five tips for getting started.
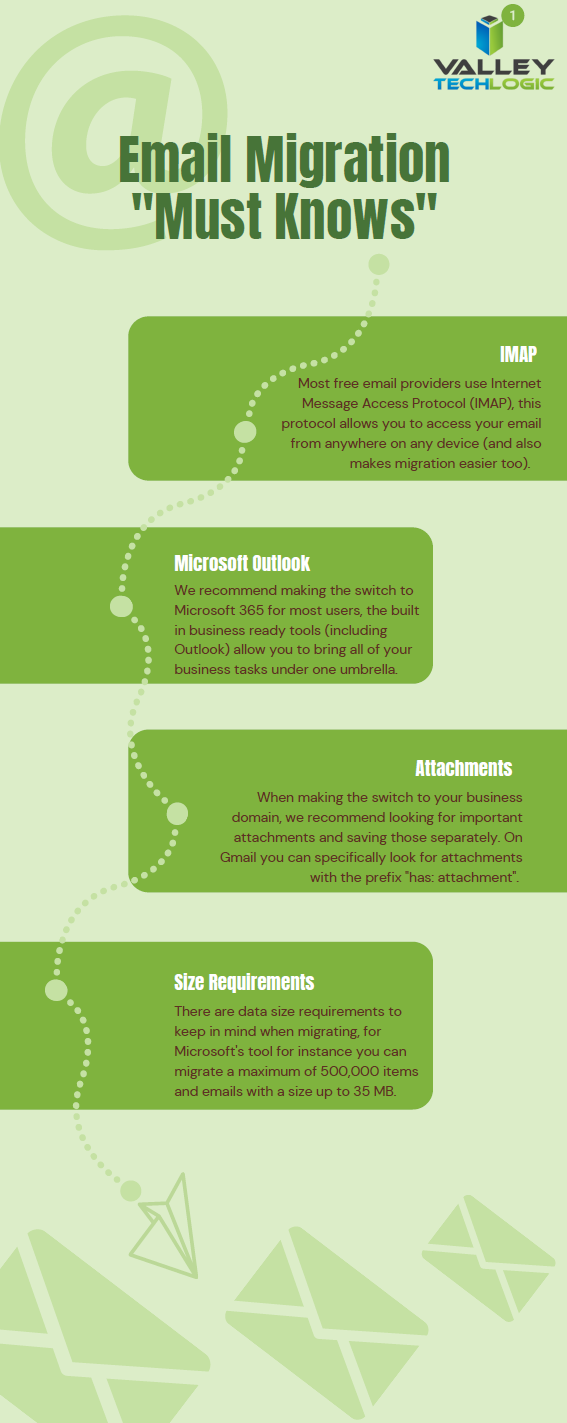
- First, make a list of the emails that will need to be migrated and get those users (and yourself) setup with work domain emails.
- Next, backup your existing email boxes data. Many free email providers offer a way to backup your data. For Gmail the steps are: 1. Navigate to “Privacy and Personalization” and click on “Manage or Delete Your Data” and click “Download Your Data”.
- Consider using a service to help with the migration, there are online services for assisting with email migration.
- Individually save any emails you can’t afford to lose. We suggest saving any especially important emails or their context individually somewhere else. Also, if you’ve been relying on your free inbox to manage important data now may be a good time to think about getting a backup program in place for your business.
- Consider bringing in the professionals, if you’ve been using your free email account for a very long time and there’s too much at stake if something were to go wrong, we suggest reaching out to a professional team to make this switch for you. They will know how to make the transition as seamless as possible.
If your business is located in the Central Valley, we have experts that can assist you with your email migration goals and taking steps to better secure your business’s data. Reach out to Valley Techlogic today to learn more through a 10-minute consultation.
Looking for more to read? We suggest these other articles from our site.
-
Unsure if the person you’re interacting with may be a fake? This Chrome extension can detect fake profile pictures with 99.29% accuracy
-
The Massive Internet Outage and The Human Error Behind It
-
Your IT Guy Quit, Now What?
-
The ransomware attack crippling a major repair firm that no one’s talking about
This article was powered by Valley TechLogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.





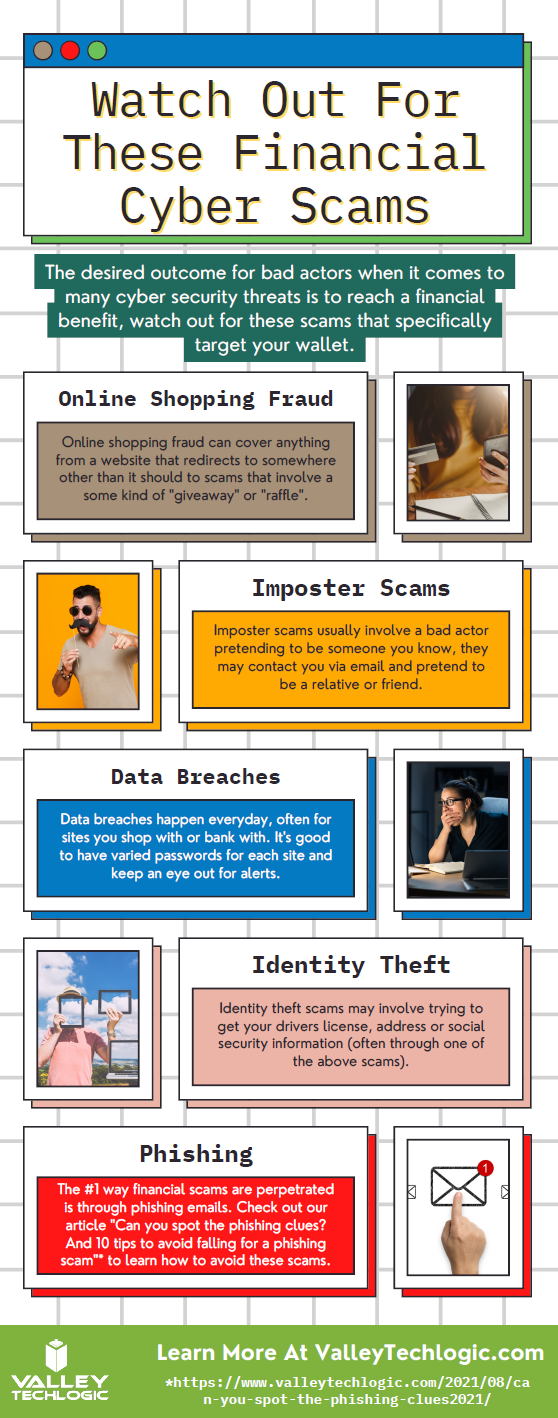



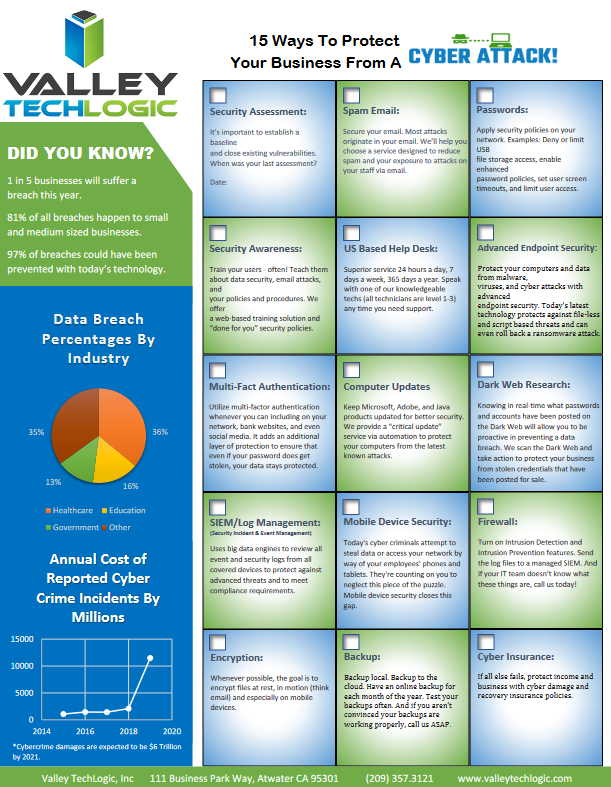




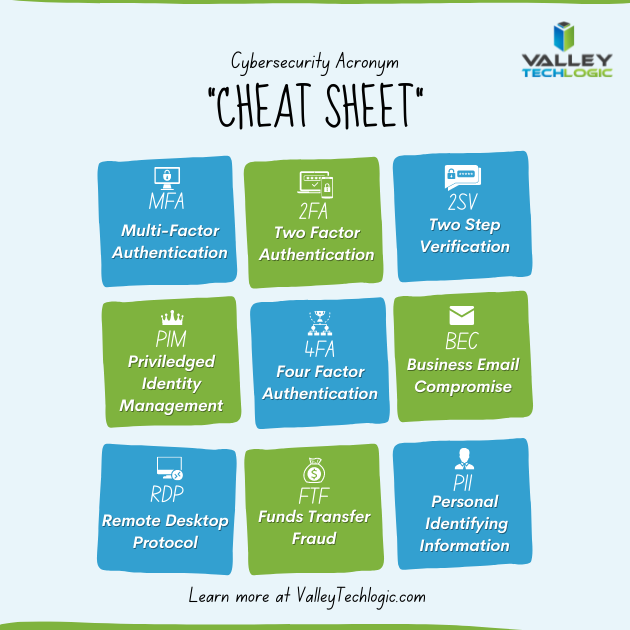 With breaches being ever more common, having that additional step past just a password before a hacker can access your account can make all the difference. A password you use across multiple website (which is also a bad idea) may be leaked without you even being aware of it, and the prompt from a multi-factor authentication application may even be your first clue that your accounts are being accessed by someone other than yourself.
With breaches being ever more common, having that additional step past just a password before a hacker can access your account can make all the difference. A password you use across multiple website (which is also a bad idea) may be leaked without you even being aware of it, and the prompt from a multi-factor authentication application may even be your first clue that your accounts are being accessed by someone other than yourself.